Understanding and regularly reviewing Microsoft Exchange's default settings is crucial for optimal user experience and system performance. While designed for simplicity, these defaults include essential security measures that may need updating to address evolving cybersecurity threats. An effective Exchange security checklist should incorporate authenticity verification (e.g., MFA), regular security audits, access control policies, data encryption, and staff training. Customizing default settings, such as mailbox limits and spam filters, allows administrators to optimize system performance while enhancing data security. Following best practices, including iterative testing and staying informed about industry standards, ensures a robust and secure Exchange environment.
In today’s digital landscape, understanding default settings is crucial for enhancing exchange security. This article guides you through the intricacies of an Exchange security checklist, focusing on key components essential for robust protection. We explore common defaults that require assessment and modification, and share best practices for customizing configurations to fortify your exchange environment against potential threats. By implementing these strategies, you can ensure a secure and efficient digital ecosystem.
- Understanding Default Settings and Their Impact
- Key Components of an Exchange Security Checklist
- Common Defaults to Assess and Modify
- Best Practices for Customizing Default Configurations
Understanding Default Settings and Their Impact

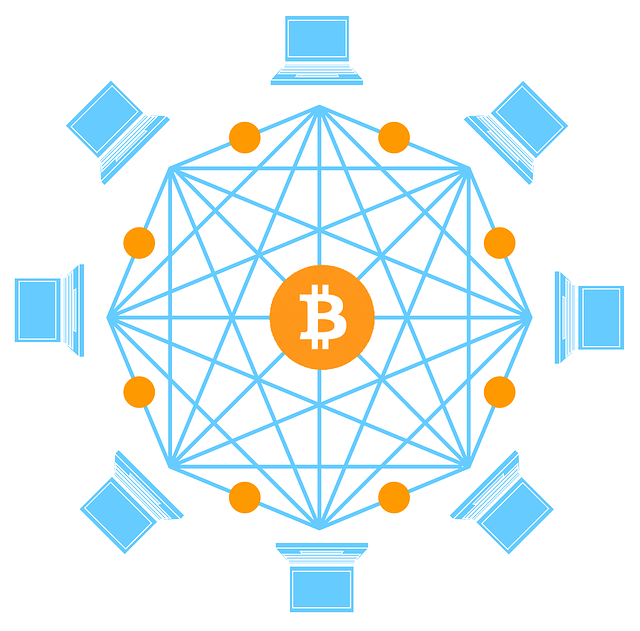
Understanding default settings is crucial as they significantly impact user experience and system performance. These pre-configured options are designed to simplify initial setup and provide a seamless starting point, but they can also pose potential risks if not carefully considered. Default settings often include essential security measures, such as those outlined in an exchange security checklist, which protect against common threats.
However, with the ever-evolving nature of cybersecurity, what was once considered a secure default setting may become outdated or less effective over time. It’s important for users and administrators alike to regularly review and update these settings to align with current best practices and address emerging vulnerabilities. This proactive approach ensures that systems remain robust and resilient against evolving threats, enhancing overall security posture.
Key Components of an Exchange Security Checklist
When crafting an exchange security checklist, several key components must be considered to ensure robust protection. Firstly, authenticity verification is paramount. This involves implementing strong authentication methods like multi-factor authentication (MFA) to confirm user identity and prevent unauthorized access. Additionally, regular security audits are essential to identify vulnerabilities and assess the effectiveness of existing security measures.
Moreover, an access control policy should be established to define who can access sensitive data and under what circumstances. Encryption techniques for data at rest and in transit are also critical to safeguard information from unauthorized access or interception. Regular security training for staff is vital to raise awareness about potential threats and ensure everyone understands their role in maintaining a secure exchange environment.
Common Defaults to Assess and Modify
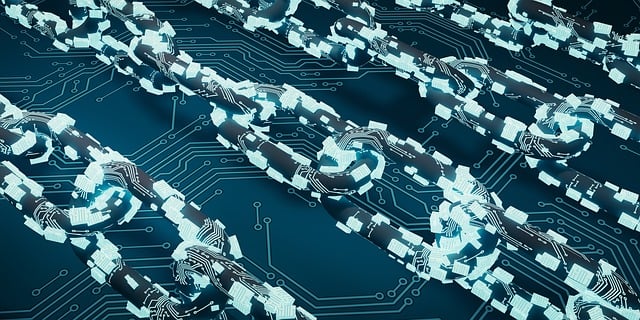
In any system or software, defaults are pre-set options that simplify user experience by providing a starting point. However, these defaults often require assessment and modification to align with individual needs and security standards. For instance, in an Exchange environment, common defaults include mailbox size limits, data retention policies, and spam filtering settings. An integral part of system management involves reviewing these defaults as they can significantly impact user productivity and data security.
An effective Exchange security checklist should include regular audits of such defaults. Modifying default settings allows administrators to fine-tune the system according to organizational needs, enhancing overall security. For instance, adjusting mailbox size limits can prevent storage issues while implementing stricter spam filters improves email safety. By taking a proactive approach and customizing these defaults, organizations can ensure a secure and efficient digital environment for their users.
Best Practices for Customizing Default Configurations

When customizing default configurations, it’s crucial to follow best practices that ensure both functionality and security. Start by thoroughly reviewing the default settings to understand their purpose and potential impacts. This involves consulting documentation, understanding industry standards, and considering your organization’s specific needs. Implement changes iteratively, testing each modification in a controlled environment before deploying it to production.
Leverage an Exchange security checklist to validate your customizations. This checklist should cover access control, data encryption, and logging mechanisms to ensure that your configurations meet security best practices. Regularly update and maintain these settings as new threats emerge and technology evolves. By adopting these practices, you can create a robust and secure environment while leveraging the benefits of customized default configurations.
In conclusion, understanding and customizing default settings are pivotal steps in enhancing exchange security. By familiarizing yourself with common defaults and implementing best practices, you can significantly strengthen your exchange’s protection. An extensive Exchange security checklist serves as a valuable tool to ensure no crucial aspect is overlooked. Remember, a well-configured system is the first line of defense against potential threats, making it an essential task for any IT professional to prioritize default settings in their security strategy.